JIT Provisioning
Provision organization membership using Just-In-Time user provisioning.
JIT provisioning automatically assigns user membership to an organization when a user authenticates for the first time. It is helpful to provide access to an organization’s resources without manual entry of all users by the IT admin.
Domain-captured users can be automatically added as members to an organization using JIT provisioning. This is useful when your application or a specific organization wants to automatically gather a set of individuals to the same workspace based on email domain.
When a user who hasn’t signed in previously through their SSO IdP enters their email into the sign-in form, WorkOS APIs detects that their email domain matches the domain of the organization and offers authentication through SSO. This user is then JIT provisioned, and future sign in attempts detect that this user belongs to the organization.
This will not work for guests, who are members of an organization but are not domain-captured by the organization.
When an IT admin adds a guest email address that does not match the organization’s domain to their SSO IdP, the guest cannot sign in for the very first time through the IdP because WorkOS doesn’t have an association of this email address to the organization.
An example scenario is an IT admin who wants to gate all contractor access through their IdP (to provide access revocation across applications) but the contractor wishes to use their own email address.
Invitations can be used to enable this scenario. By inviting the contractor to the organization, the authentication flow will detect a possible SSO connection and offer authentication through the SSO IdP when signing in.
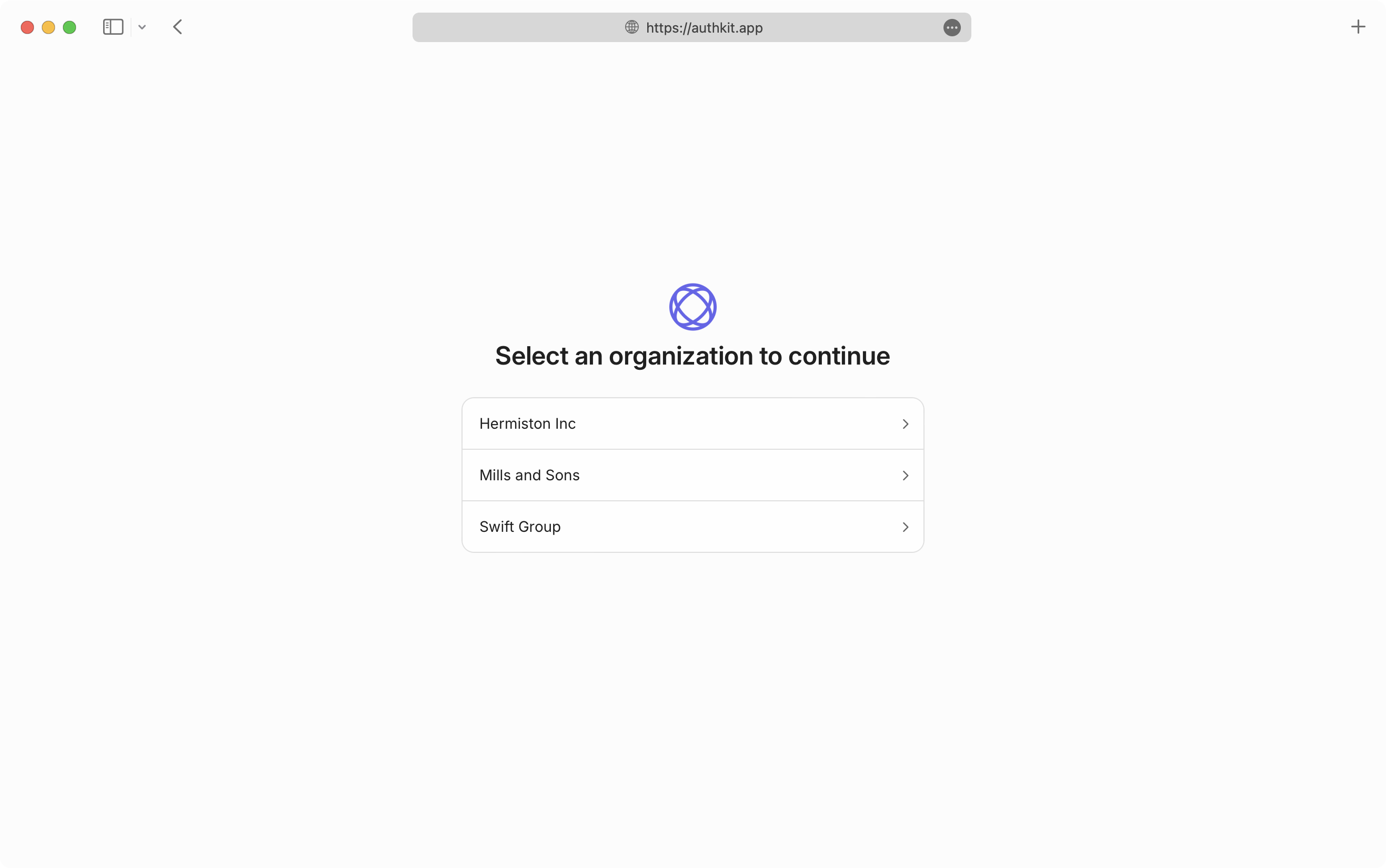
A domain-captured user of one domain-verified organization that requires SSO may be a guest of another domain-verified organization that also requires SSO. If the user is a member of both organizations, that user has two SSO credentials, and will need to choose which organization to access at sign-in time before being redirected to the corresponding IdP.
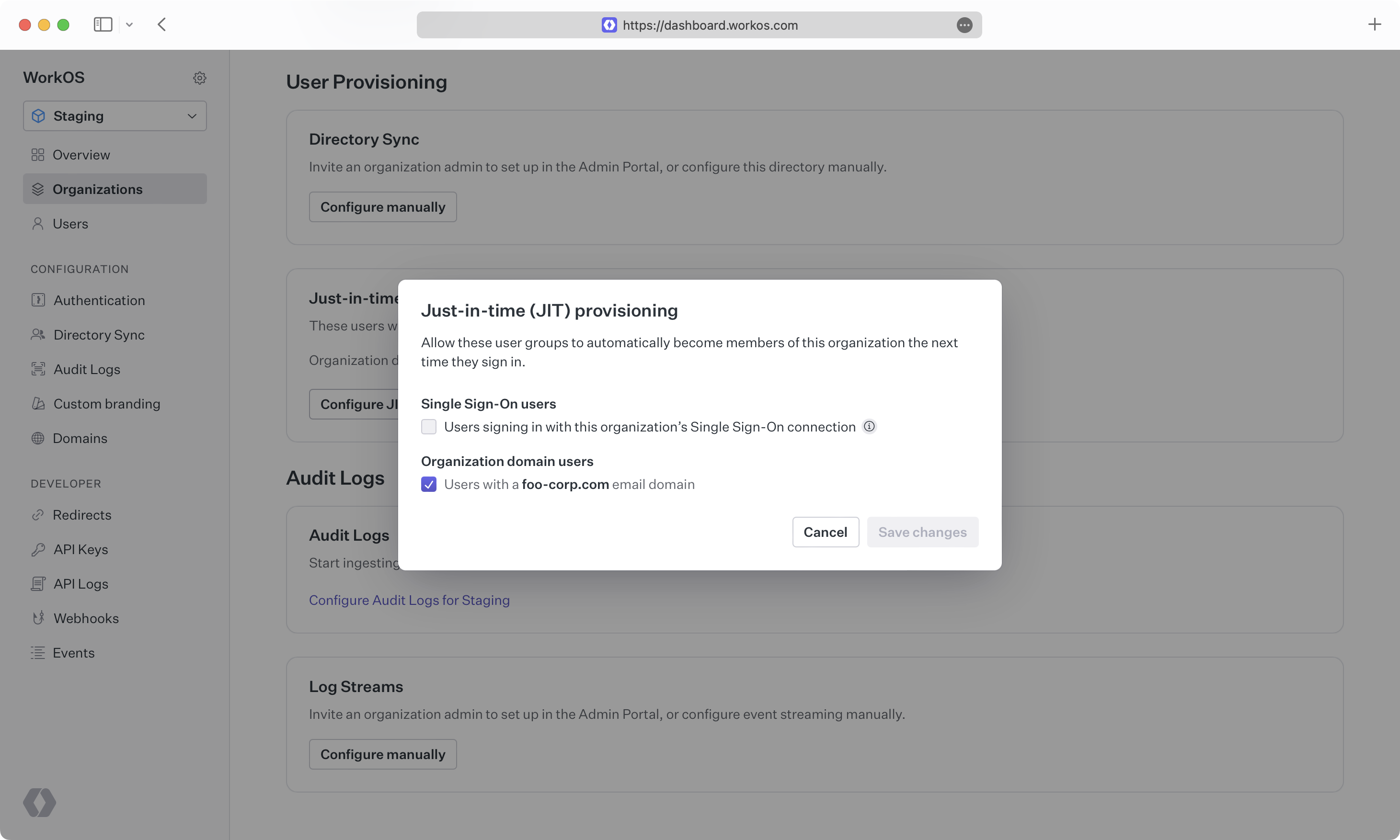
JIT membership provisioning can be disabled, if for example the IT admin wants only select individuals to have access to the organization.
When JIT provisioning is off for a domain-verified organization, new users with matching email addresses cannot be created in a self-serve manner.
Turning off JIT provisioning disables user provisioning for new users. This may be useful when an organization wants to limit access to its workspace. Invitations can be used to allow specific email addresses to sign up and be provisioned.